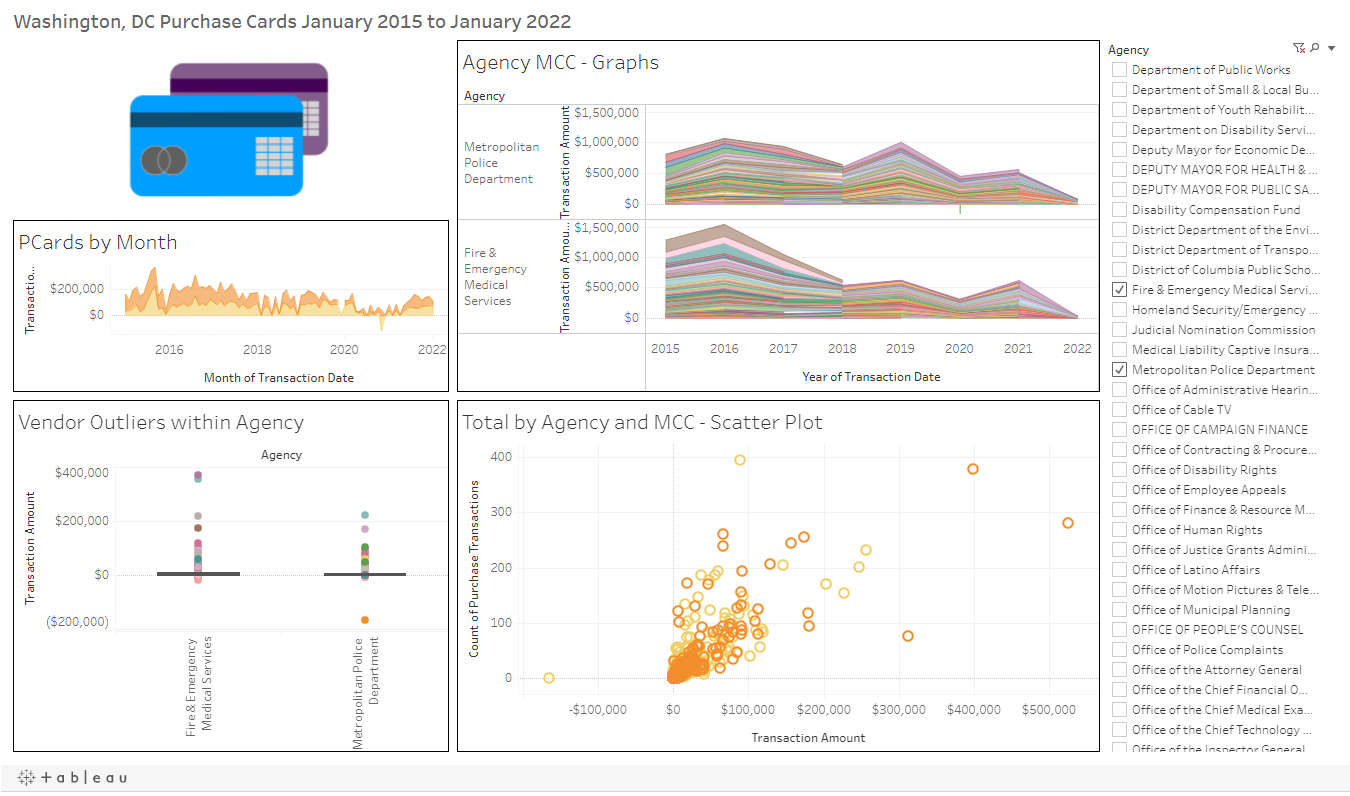
Purchase Cards – Quick Start

The World of Purchase Card Fraud
How can organizations avoid purchase card fraud but still take advantage of the ease of using credit cards to acquire the goods and services they need? Many organizations have some protections already in place. They develop internal policies to limit purchase card use to designated buyers, products, or situations. They require their employees to read and sign their “Purchase Card Use” policy. Employees promise they will use the card for only appropriate business transactions and never for personal, non-work use. In an ideal world, these protections should allow organizations to gain the benefits of simplified purchasing without experiencing any issues of purchase card fraud.
In our world, however, misuse of purchase cards occurs frequently.
- Network Engineer at Verizon – February 2022
- Medical Center Supervisor at the Cleveland Veterans Affairs (VA) – October 2021
- School District Administrator at the Little Rock, Arkansas School District – February 2022
- Training Coordinator at Sandia National Laboratories – December 2021
- Planning Manager at HP, Inc – March 2022

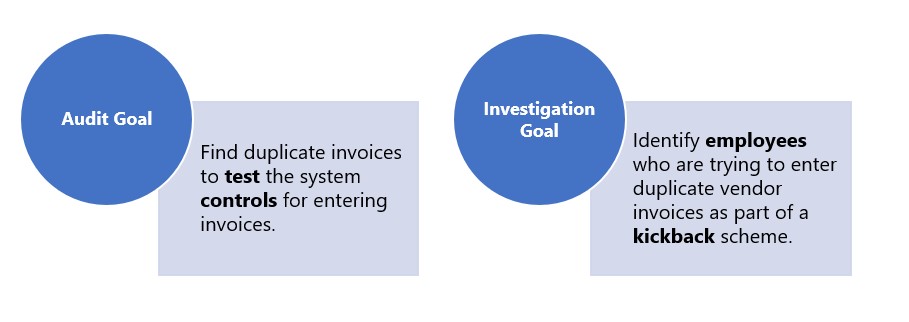
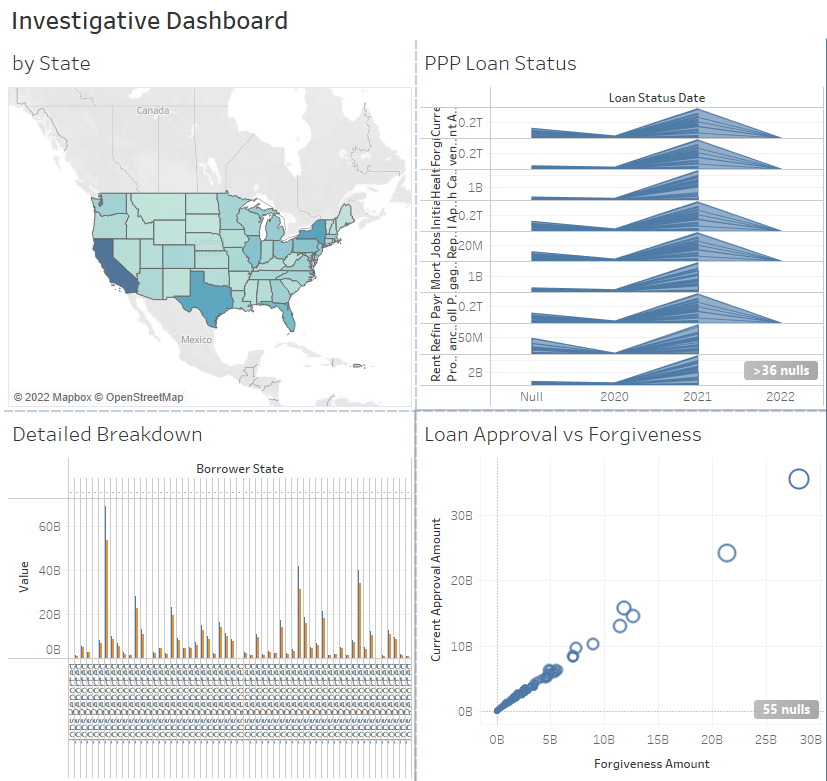
Identify – Business Questions and Available Data
Business Questions
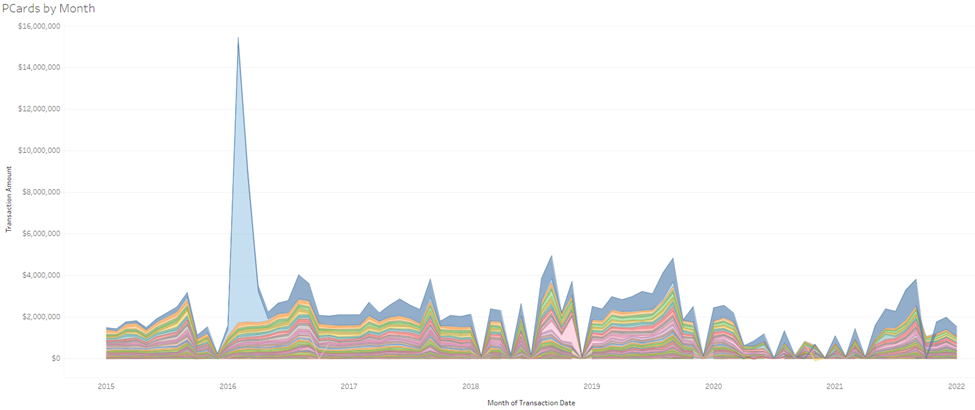
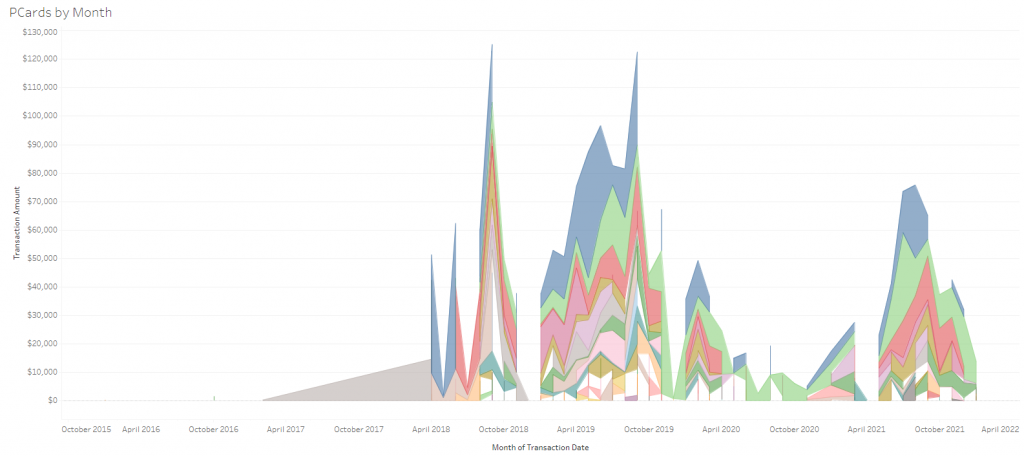
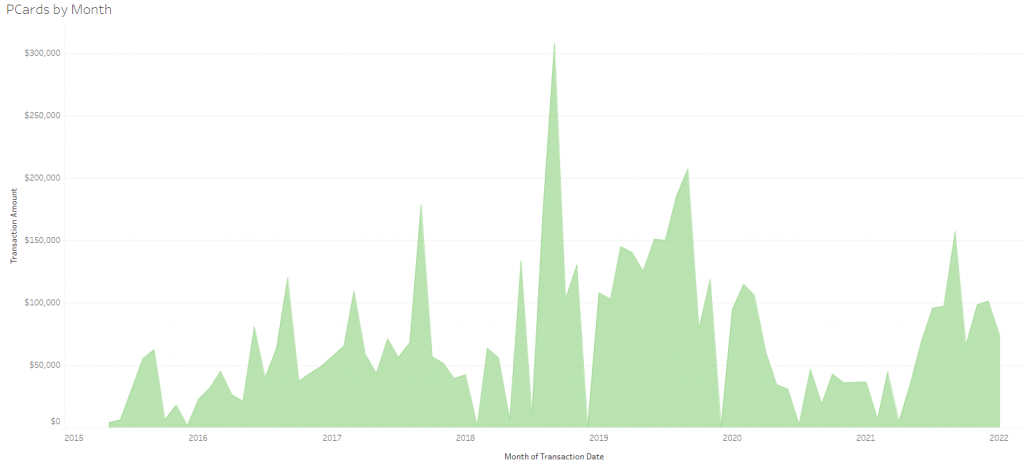
If your organization issues purchase cards to more than just a few people, you likely have access to a comprehensive data set that you can use to evaluate risk and detect potential misuse or even fraudulent activities. What type of concerns do you have regarding your purchase cards? Do you think employees might be making personal purchases? Are you concerned that suspicious vendors are receiving payments? Which of your departments does the most purchase card spending? Are there opportunities to reduce costs by negotiating contracts with your frequently used purchase card vendors? Are some purchase agents “splitting” transactions to buy things under the established approval limits? When employees ship purchases to your organization, are they sent to valid addresses? Have any of your purchase cards been compromised and are now available on the dark web, risking purchases by external agents who have stolen your employees’ identities? Do you want to quickly identify anomalies in spending so that they don’t balloon into a multi-year fraud scheme?
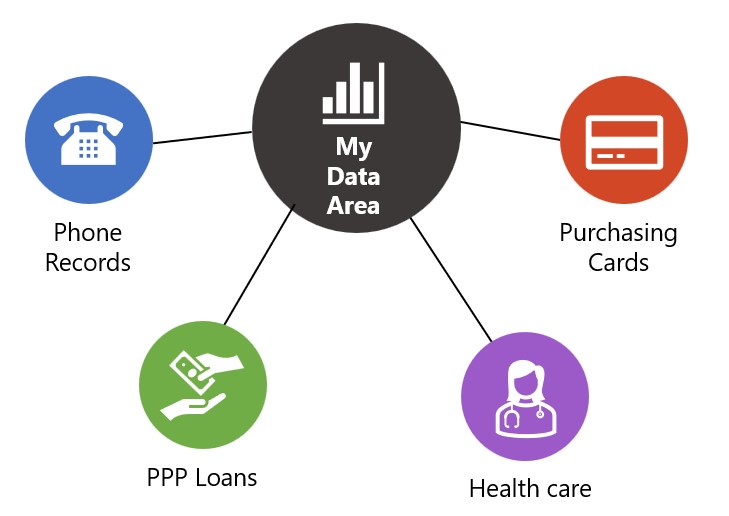
Available Data
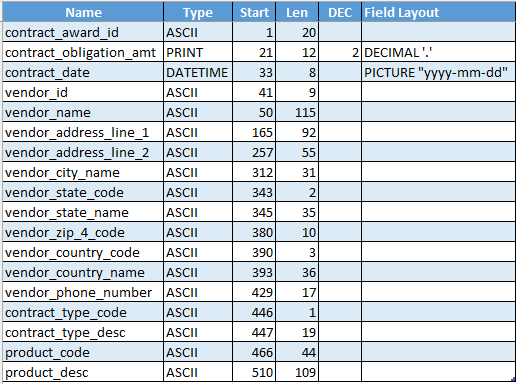
Where can you find the data to help you answer these concerns? Purchase card data can come in various formats. I’ll cover some of the most useful and widely available here. However, if your data is slightly different than what I’ve mentioned, do not worry; you can likely still use it in analytics. The best data is accessible periodically and is in a consistent format such as these:
-
- Data Set Format – Monthly Credit Card Feed
The ideal data set would be a monthly feed of data from the credit card company that includes all features of the purchase transaction, including, at a minimum: the cardholder’s id, name, transaction date, vendor name, and transaction amount. It is also beneficial if additional data is available about the transaction. These fields could be Merchant Category Code (MCC), transaction description, online purchase indicator, or other vendor metadata. You may need to download this data monthly as a comma-delimited file (*.csv) from the credit card company’s website. The act of downloading the data, once you incorporate it into your routine, could further be simplified using robotic process automation (RPA).
- Data Set Format – Purchase Approval System
Another ideal data set could come from your purchase approval system. It may be your organization’s policy that all purchase card transactions need to be approved, and there is a system that facilitates this process. If this is the case, you will have all of the monthly credit card feed data fields listed above. Plus, you will have other fields such as approver id, approver name, and approval date. Then, take a look to see if you can capture and match to some additional vendor information from your internal vendor master file. Finally, if the approval system stores copies of receipts supporting the purchases, you will more easily be able to perform follow-up investigations into possible anomalies. Be sure to retrieve the most granular data available, down to the transaction line item, if available.
- Data Set Format – Monthly Credit Card Statement *.pdf
A less-than-ideal data set, but one that provides the same basic information as data set number 1, would be a *.pdf monthly billing statement sent by the credit card company that is received electronically or is downloadable. The electronic *.pdf file can be ingested by different data analytics software programs, although the initial import is a bit more complicated than a text-based *.csv file. However, once you establish the process and define a standardized import, the next month’s import should be straightforward to automate.
- Data Set Format – Monthly Credit Card Feed

Other Concerns
Analysis Frequency
If the layout stays the same from period to period, you have the opportunity to build a process that allows you to monitor purchase cards on an ongoing basis. The ideal way to stay on top of purchase card risk is to perform analysis on a continuing basis. However, the first run-thru of the data can start with whatever large file you have available. For example, if your credit card company allows for an 18-month historic download, start with that. Keep in mind that once you perform the initial analysis, you will want to continue the analytics each subsequent month.
Protect your Data and Yourself
You may notice that I did not include the credit card number as one of the data fields you would want to include in your data set. If you have the cardholder’s name or id, you probably have enough information to analyze individual purchasers, even if the cardholder uses more than one purchase card. Actually, even if you don’t have the cardholder information, you can still perform analysis, as shown in the included case study. However, there is a practical reason that I did not include this information. The laws surrounding the possession and security of credit card numbers are plentiful. There are different laws and penalties under state laws that penalize abuses of this information.
For example, Virginia has strict laws governing credit card numbers. The simple possession of two credit card numbers can indicate a violation of the law. Federally, the FTC limits the information that can be stored by merchants about customers’ credit card numbers. The primary reason for this is to protect the numbers so that they are not revealed to fraudsters. That’s why you typically see only a portion of your credit card number on all receipts. Credit card number limitations extend to the way they are stored in databases. As you handle this information, take the necessary precautions to protect it. Do not accumulate a treasure trove of credit card numbers that could be stolen. Ensure secure storage and transfer of all credit card information. If you have the credit card number, please take care to obscure the numbers entirely or at least limit the digits shown.